You Won't Find The Key Under The Doormat
Using the internet we all surrender our information (both sensitive and unimportant) to online applications that eventually dump them in a database.
If you think your information is safe in the database, think again.
Obviously there is a general problem with access to these databases that can render information resting there insecure. The problem arising with most online applications is that most of them use passwords to access the database that are stored unencrypted on the server.
Even for commercial online applications it is quite common to store the crucial password that grants access to all data resting in a database in a simple configuration file, in clear text. For example, Magento, the well known online shop software, stores the database password in the file "app/etc/local.xml" where it shines in all its glaring plain text glory.
Of course you can start to secure these files. It's the most natural thing to do. And you have to do it, fast. Because under normal circumstances, these config files are readable for everyone on the server when the default installation has finished. Most online applications seem to rely on the fact that the administrator knows that there is work left to be done. Following the principle of least privilege is a good guide to make those sensitive files as secure as possible on the server. But let's be honest, relying on the assumption that no unauthorized person will ever see the content of such a file may not be prudent.
It's a little bit like putting the key under the doormat.
Getting More Protection For Your Information
It doesn't really help in this situation to use the encryption functions built into the database, because these require a secret key to work. As this secret has to be provided from outside the database, where should it be stored? Under another doormat, of course. All attempts to solve the security problem with a secret key for internal encryption lead back to the problem we already have with the database password. There simply is no good way to store it.
If you've read my article about the secrets of email encryption you already know that there is a method of encrypting data that does not need such a secret, we have double key boxes today. We can use public keys to encrypt information before it is stored in a database, there is no secret required to do that. Any sensitive information can be protected that way before it enters the database.
A secret information is only necessary when a person needs to use the information that is stored encrypted in the database. Let's take the obvious example of financial account information. There is no need to store this information in clear text in a database, because the moment a staff member needs this information to carry out a money transfer, it is possible to recover the financial information by decrypting the database entry. The staff member has a brain to store the individual secret needed for decryption, and he has a reason to use the database entry now. The financial information can remain encrypted in the database when it is not actually needed to act upon it.
PhpMyAdmin is the most popular tool to work with MySQL databases easily, so it's only natural to apply encryption to databases by extending this popular software with the Web Encryption Extension. With the newest version 1.1 it is now possible to process a number of different inputs in a flexible way. Before, say, an encryption is carried out the name of the input textarea has to be determined and the user must be able to select the database field he wants to encrypt, beforehand. We decided to introduce the "flexible mode" into the Web Encryption Extension, which makes pre-selection of the input field possible via a simple menu next to the encrypt button.
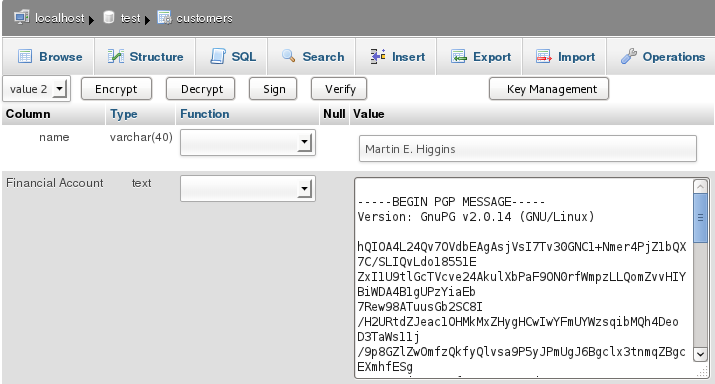
The selection menu (top left) can be tailored to show only the database fields that are intended to be encrypted.
Upgrade Your PhpMyAdmin Installation
Web encryption has proven successful with webmail and it's time that database installations follow suit. Having the ability to encrypt selected database fields with the push of a button can only improve online security. To make an upgrade of your PhpMyAdmin installation as easy as possible for you we have bundled a tar archive that contains everything you'll need in one single download. All the software in this download is licensed under the GPL, of course. And upgrading is merely a matter of extracting the archive and providing a safe place for the public keys on the server. Finally you will need to adapt the selection menu in which the options for encryptable data fields show up. All this is done by editing a single file. We've prepared a comprehensive guide for you to do the necessary steps yourself and an online demonstration to see how it works.PhpMyAdmin will let you do whatever you want with your database and this includes public key encryption by now. But we have to take the process one step further, as your database represents the foundation of another web application. Your encrypted database fields will be used here and a means of decryption has to be built into this second application, too.
Your roll-out of encryption won't stop with phpmyadmin, but at least you won't find the key under the doormat, ever.
posted on 2nd March 2012